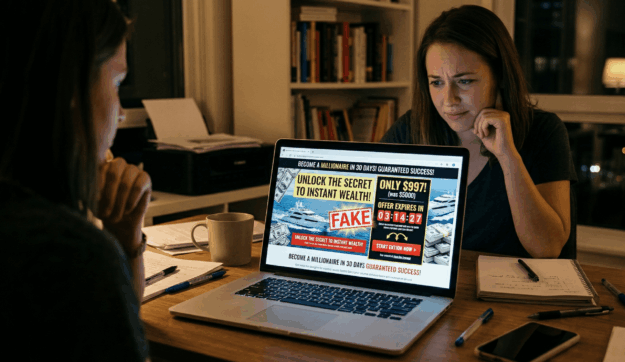
Online Course Scam: How to Spot Fake Courses & Stay Safe
The e-learning boom has a dark side. The online course scam is now a full-blown industry. Beyond bad advice, many online gurus now use their platforms to spread malicious software. The FTC’s 2025 Ransomware Report highlights how tech support scams and malware-based attacks continue to target consumers. Here is how to spot the scam before…