History
Trojan (Trojan horse) deserves its name well. Like when the Greeks leaving behind a large wooden horse as a victory offering, it was in reality a trap since the horse contained soldiers. Software trojan horses use the same model, presenting themselves as innocuous or beneficial but are in reality malicious. There is no real consensus when the first trojan was developed, but the first ones were unsophisticated pieces of software. Current ones are powerful foes, often hard to remove.
How do they work ?
Trojan horses usually use social engineering, like a pirated software or a fake Office document send by mail, to gain control over a computer. Once installed, they usually hide themselves from the system and make it impossible for the user to remove. Their functionally know no end, but they are able to spy on the user, send spams, make attacks, mine using the compromised computer resources, etc.
Current situation
Since the hardening of Code Signing with Windows 7, trojan horses are much easier to detect and remove. However, due to their evolved functionalities, they still account for a large threat. Nowadays, trojans with mining-engines are ones of the most common malware in the wild.
In the Wild
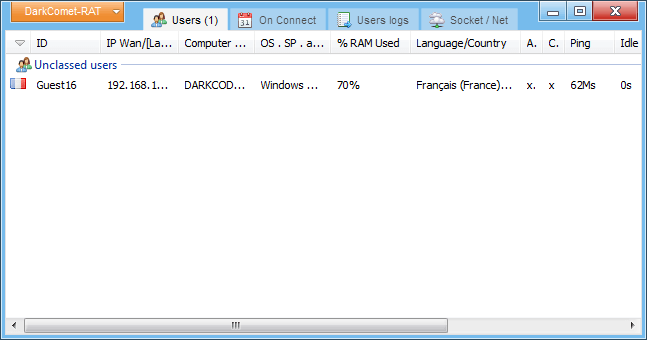
One of a well-known trojan horse was named DarkComet. It was initially made public in 2008 for legit situations where a user wanted to remote-access its devices. However, since 2012, it became a full-fledged weaponized trojan being users from newbies hackers to sponsored-states agencies.
How to remove a trojan ?
There is a saying on the Internet saying “If the product is free, you are the product”. Although inaccurate (open-source software is quite the exemple), it is far from being wrong. Never execute or install activators/cracks/keygens or the like and be wary of the source of the software you install. Be especially on guard with dubious email messages which may be the source of infections.
RogueKiller, in its Premium version, offer a very effective real-time protection module. You can also try our general malware removal guide.