What is a Trojan ? How to Remove ?
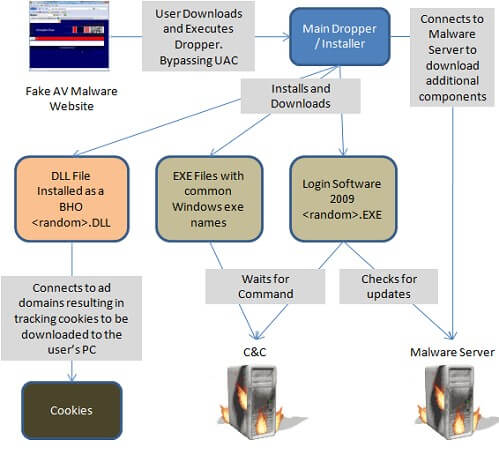
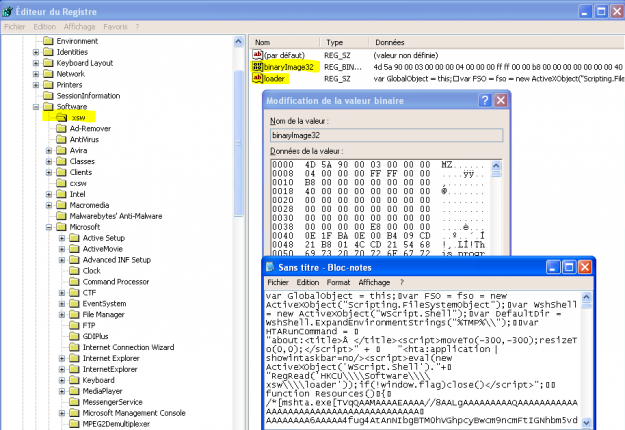
Trojan horses usually use social engineering, like a pirated software or a fake Office document send by mail, to gain control over a computer. Once installed, they usually hide themselves from the system and make it impossible for the user to remove.