Founder and owner of Adlice Software, Tigzy started as lead developer on the popular Anti-malware called RogueKiller. Involved in all the Adlice projects as lead developer, Tigzy is also doing research and reverse engineering as well as writing blog posts.
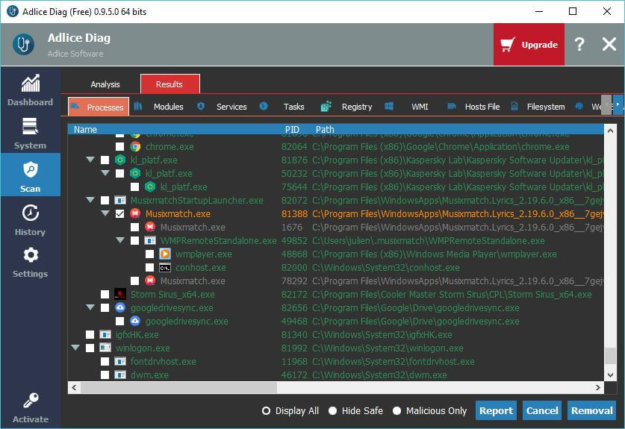
We are proud to announce that our new project, that we’ve been working on hardly for the past year, has been released ! It is called Adlice Diag, and it will be your favorite software when it comes to diagnose a machine’s health…
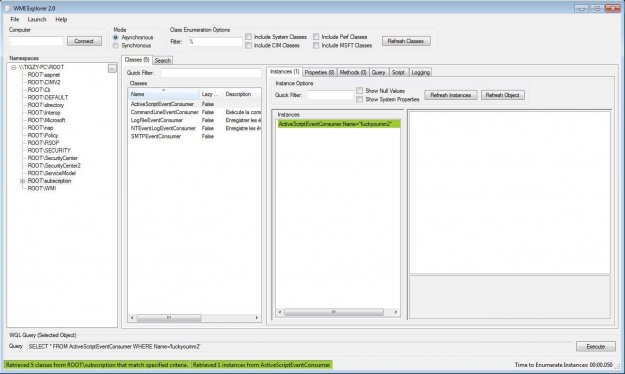
Infections related to the use of hacktools like Windows Loader or KMSPico are rising. Learn how malware authors use them to spread cryptominers, ransomwares and ultimately take control of your newly installed operating system.
Alpha bay, Silk Road, Hansa: They made the headlines of newspapers for weeks. They were underground markets offering several illicit goods and services and were shut down in 2013 and 2017. All were using Tor, currently the most used parallel Internet network, called Darknet. DARKNET Computers connected to the Internet use the Internet protocol suite…
A major increase in the number of malware featuring cryptominers has been observed. Discover the way malware writers make money with them.
If you are a hacker, you probably already know about mimikatz. This tool is widely used by hackers to retrieve passwords. Learn how to use.
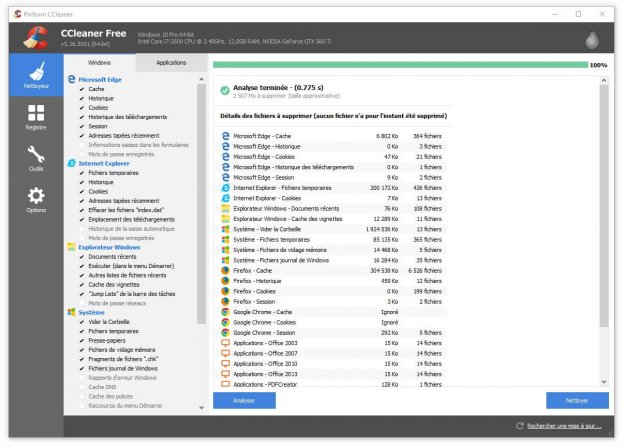
Popular cleanup tool CCleaner was compromised to deliver the Floxif malware. Learn how this happened and find if you are at risk.
Infected with Adware.Lsmo ? Follow this step-by-step guide for malware removal of the Adware.Lsmo infection and clean your machine.
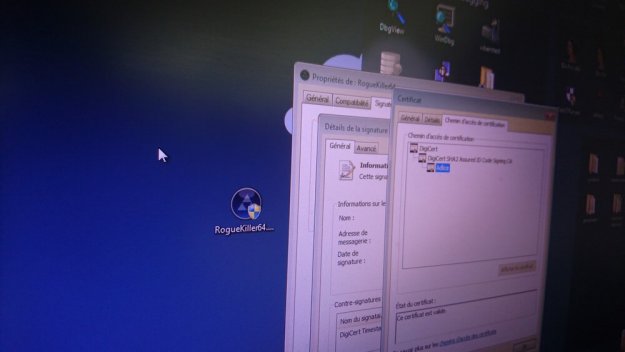
Code signing is required to load drivers in Windows. Also, they tell users if an application can be trusted and launched. Learn how it works.
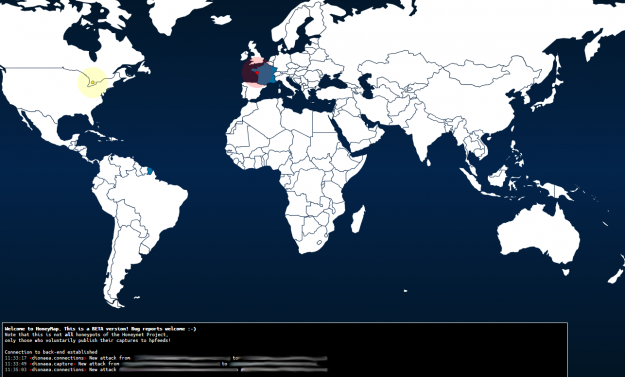
Catch malware with your own Honeypot – Learn how to deploy a honeypot in 10 minutes with this step by step guide about Cuckoo sandbox. Easy sandboxing.
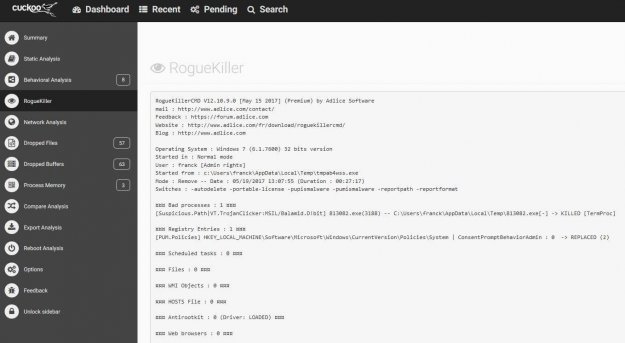
Get an anti-malware removal report with a very simple cuckoo sandbox customization. Learn how Cuckoo works and how to add custom modules.