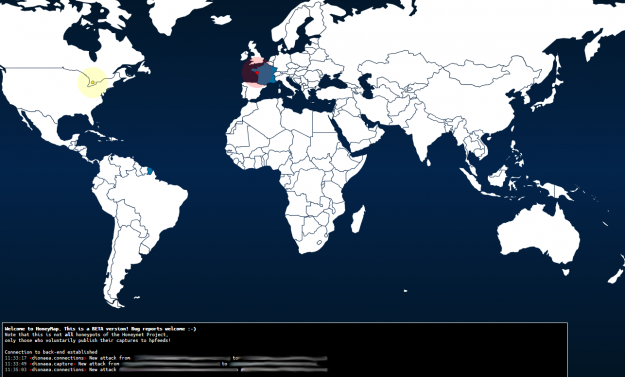
What happens on the Darknet ?
Alpha bay, Silk Road, Hansa: They made the headlines of newspapers for weeks. They were underground markets offering several illicit goods and services and were shut down in 2013 and 2017. All were using Tor, currently the most used parallel Internet network, called Darknet. DARKNET Computers connected to the Internet use the Internet protocol suite…