Founder and owner of Adlice Software, Tigzy started as lead developer on the popular Anti-malware called RogueKiller. Involved in all the Adlice projects as lead developer, Tigzy is also doing research and reverse engineering as well as writing blog posts.
Some software monetize themselves with partnerships with other companies, and bundling their installers with optional software offers. Starting with UCheck 3.10, PUP Protection is available (BETA) and prevents optional offers to install on the system when running a setup
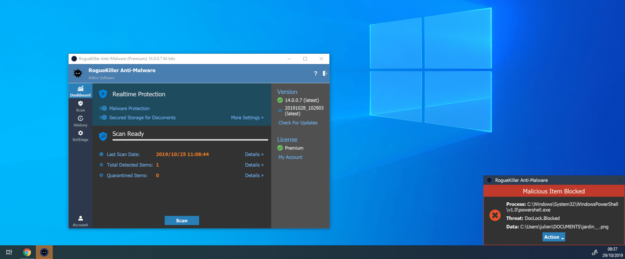
After a company is victim of a Ransomware, they are asked a ransom to recover the files and avoid them to be leaked online. This is why we have developed DLP, for Data Leak Prevention, in our RogueKiller Anti-malware product.
Computers worms are designed to leverage vulnerabilities that allow them to gain control over a device then scan the network for other vulnerable devices and so one
Trojan horses usually use social engineering, like a pirated software or a fake Office document send by mail, to gain control over a computer. Once installed, they usually hide themselves from the system and make it impossible for the user to remove.
Adware (ad-ware) are a quite recent thread, compared of the others. They begin to rise in popularity with the decline of the shareware license model. Instead of offering trial version of the software they developed, software writers began to include ads in their installers
Computer viruses were the first kind of malware that were developed. At the beginning, they were not malicious per se (the first computer virus “Creeper”, developed in 1970 only displayed a message), but soon after malicious ones begin to appear and counter-measures known as “anti-virus” software were developed.
Avec le développement des connexions Internet à large bande, les services en ligne / en nuage sont devenus de plus en plus nombreux. Vos données ne se trouvent plus seulement sur votre ordinateur, mais sur une multitude de serveurs en ligne. Vous devez non seulement envisager maintenant ce qui pourrait arriver si votre ordinateur est infecté, mais également ce qui pourrait se produire si l’un de vos comptes en ligne était compromis.
We are pleased to announce our flagship, RogueKiller Anti-malware, is finally available for version 14 BETA testing. Version 14 is a very big milestone for us because it introduces a major new feature that customers have been asking us for a long time: Real Time Protection. Let’s take a look. Real Time Protection RogueKiller 14…
We are proud to present you today a new software (or rather a new variant of an existing software) that was many times requested by our customers, UCheckCMD. Test it now !
We are proud to announce that our popular Anti-maware RogueKiller new version, that we’ve been working on hardly for the past year, has been released ! Test it now.