MRF
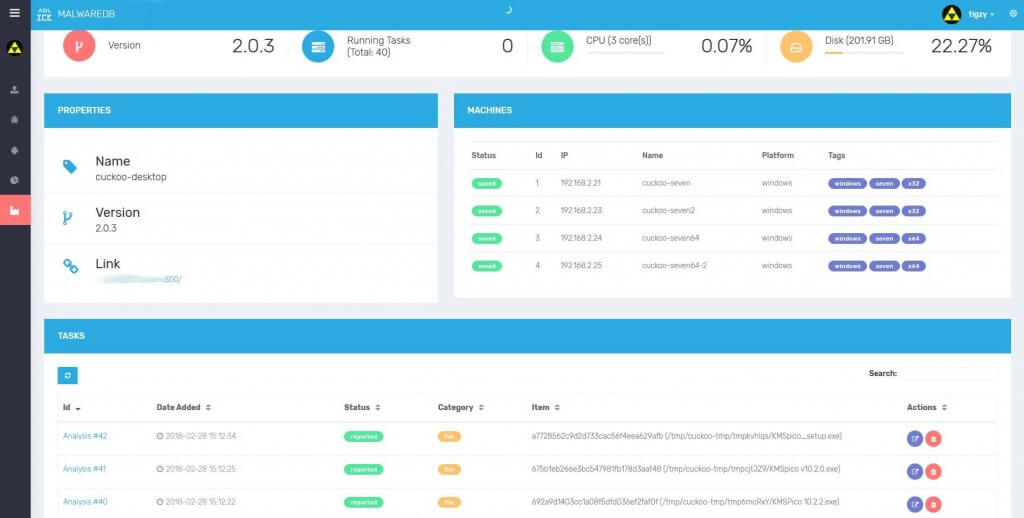
Host and manage your own malware zoo.
Premium ($57/year)
All features included
Top support priority
Enterprise Use Allowed
Email support

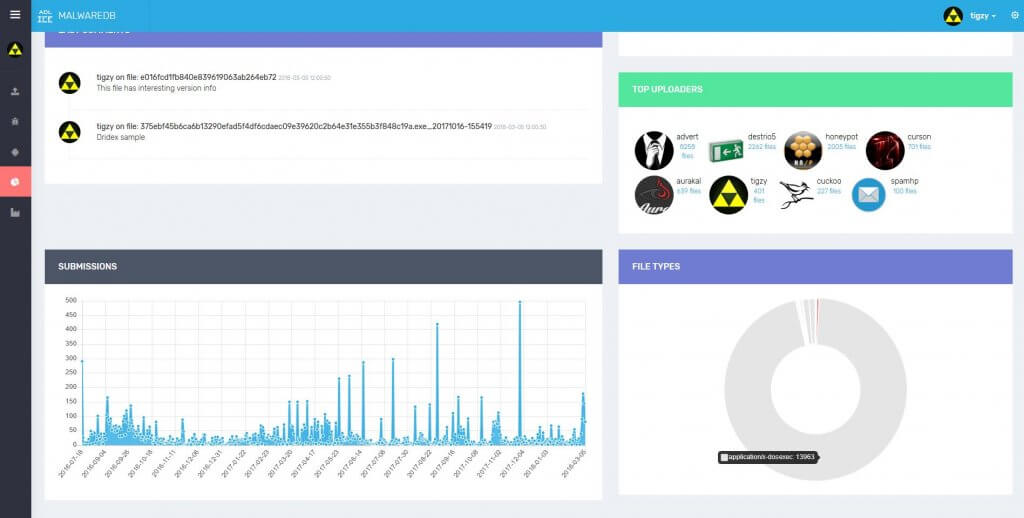
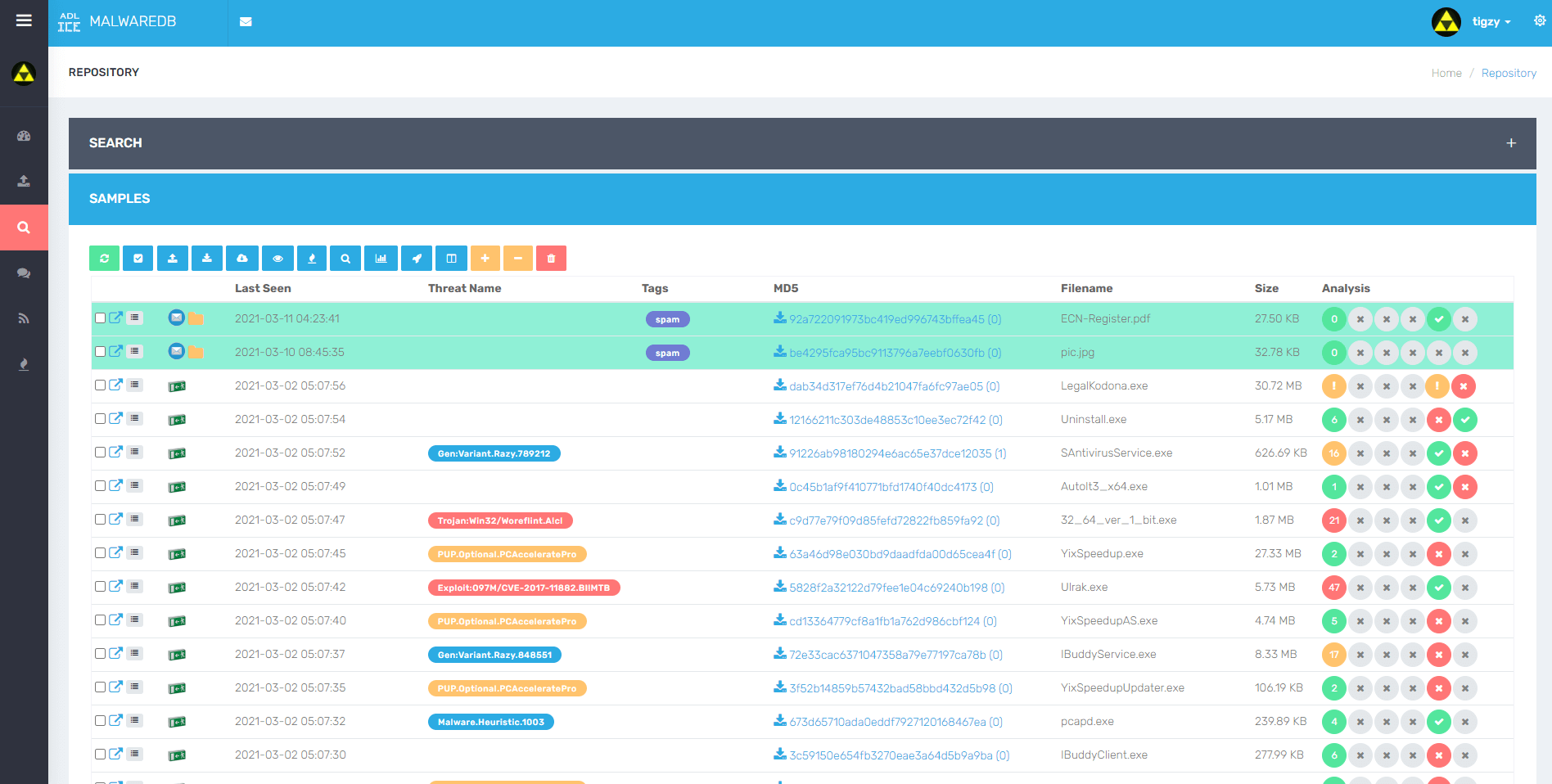
Search & Discuss
MRF provides advanced search to retrieve your favorite samples the database. Search by hash, name, or even scores and metas.
Create discussion pages to request a specific sample, or just discuss any topic.
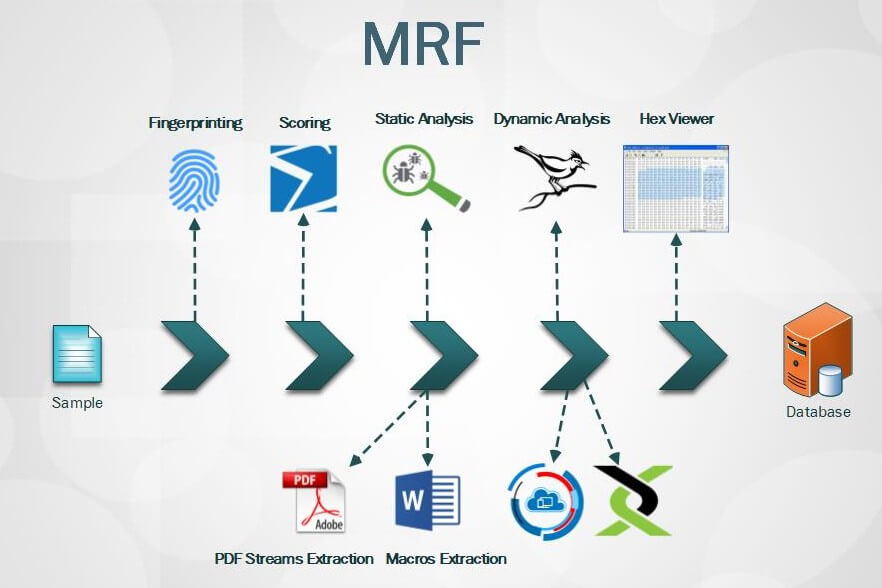
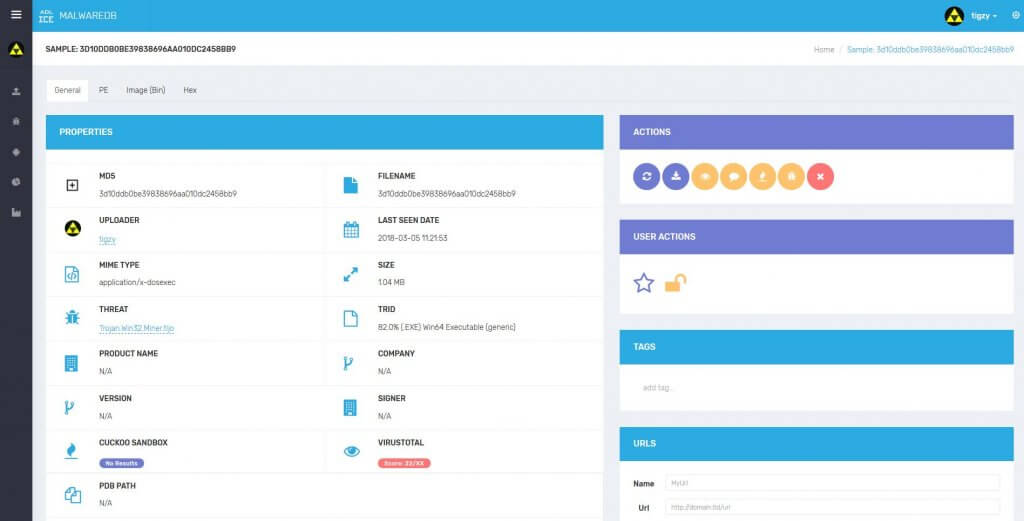
Static Analysis
When new sample is uploaded, a variety of static analysis modules are ran to extract important imformation from it.
This information is then displayed in a beautiful user interface, and can be used for search.

Dynamic Analysis
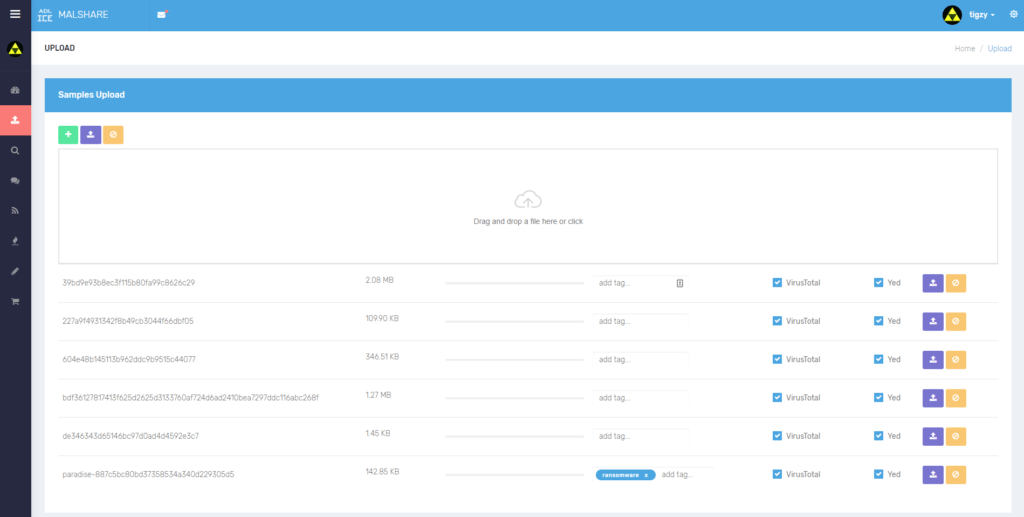
MRF provides modules for 3rd party or in-house services performing dynamic analysis, or further scanning.
Get VirusTotal, Hybrid Analysis reports or Yara signature scan results. Extract the most from your samples !
Steven A. - July 2018
A very good malware organizer
I am a researcher working in a CERT company. We are collecting hundreds of new samples every day, and we needed a way to organize and triage them locally, inside the company.
MRF has been installed by our IT department, they created our access and made the website available inside the corporate network.
Our honeypots and spam collectors are directly plugged into the framework. This is very convenient for us, they are already tagged with their source and contain useful informations in the comments. All we need to do is open them, get the information we need for forensic or intelligence, and that's it ! Very useful fo follow spam campaign and new threats. Good job !