Apocalypse now
Right now, bots are scanning the internet for mongodb database with no password, and open port. When they found some, they use that open access for saving all the data (somewhere), dropping everything, and leaving a ransom note (just like ransomware, yes) to get your data back after paying the price.
If that happened to you, it’s mostly too late, but if not please read the following and secure your database NOW!
Ransomware
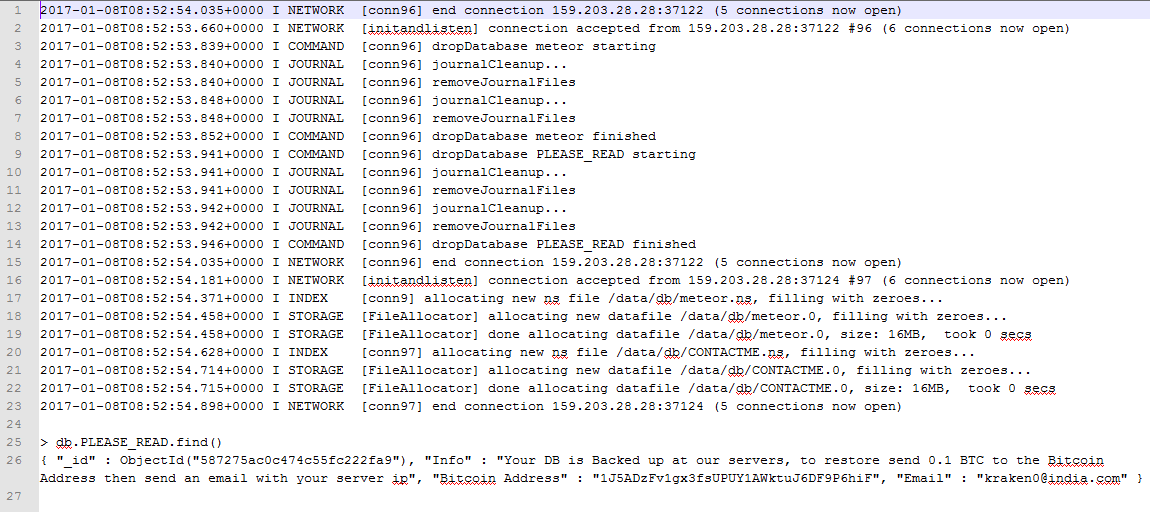
Dropping a database and leaving a ransom note is somewhat new. Here’s some logs from our honeypot where the database was dropped by that bot:
Dockerized mongodb
If you use the dockerized version, it comes pre-configured with open access to the world, and no password. This is B.A.D! To secure a dockerized version of mongodb, restrict listening address to localhost like this (put the 127.0.0.1 address before the port):
docker run --name db -p 127.0.0.1:27017:27017 -d mongo:3.0 --smallfiles
Regular Mongodb
If you don’t use docker, the best you can do is preventing the port from being accessible to the world with iptables. However, if you don’t have a firewall, or not familiar with, you can just use the bind_ip parameter to launch the mongodb instance:
bind_ip = 127.0.0.1