How to destroy small developers
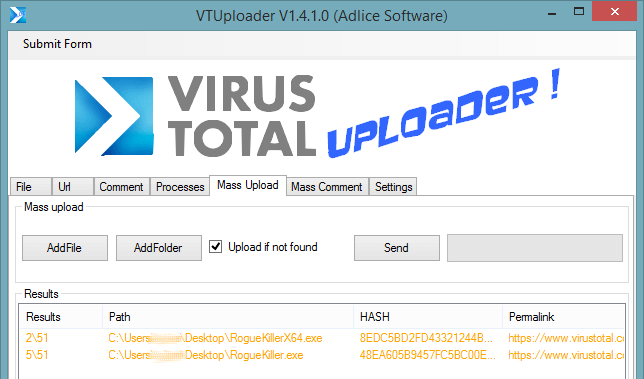
Starting with RogueKiller V9, we have a lot of issues with some Antivirus vendors, flagging our software at every release. Not because it’s a malware, but because of their heuristics engine. And overall, because they really SUCK at whitelisting legit products.
This is really annoying, let me explain why by simulating a RogueKiller release step by step:
- All starts with code changes, bugfixes, improvements. They are made and tested while the current version is still in use.
- Then the new release is pushed online
- As this is a brand new binary, never seen before, AVs are informed automatically and they analyse (automatically) the sample. Good. Well, not good actually
- Some antivirus may find some suspicious thing in RogueKiller (Yeah, that’s an antimalware with powerful search/destroy features). That means their engine is pretty good actually. But that’s a false positive anyway.
- So RogueKiller is detected by them, and their database is updated and distributed to their customers. Which will complain to me that RogueKiller is detected. Bummer.
Starting here, not a big deal. I just submit a false positive form to the AV vendor. Here’s one of them:
Hello
Could you please remove detection from RogueKiller binary / website?
Please don’t whitelist by HASH, it changes very oftenIt’s an antimalware tool known for 4 years now.
Website: https://www.adlice.com/software/roguekiller/Direct links:
https://www.adlice.com/softs/roguekiller/RogueKiller.exe
https://www.adlice.com/softs/roguekiller/RogueKillerX64.exeRegards,
And here’s the answer:
In relation to submission [3527357].
Upon further analysis and investigation we have verified your submission and as such this detection will be removed from our products.
The updated detection will be distributed in the next set of virus definitions, available via LiveUpdate or from our website at http://Xxxx
Decisions made by SXxxx are subject to change if alterations to the Software are made over time or as classification criteria and/or the policy employed by SXxxx changes over time to address the evolving landscape.
If you are a software vendor, why not take part in our whitelisting program?
To participate in this program, please complete the following form: https://Xxxxx
Good, detection will be removed. I’m happy they made it. I do the same for other vendors (that maybe copied on some major AV vendors, mmmh?) and that’s ok. For now.
10 days later….
Let’s go for another release! We push the sample online, and here’s what happen:
- Day 1: Everything is good, not detection
- Day 2: The SAME AV VENDORS DETECT US AGAIN!!! What the HECK?
- Day 3: Other “copy cat” AV vendors detect us again, because they saw the detection of the previous vendors
- …
- Day 5: After submitting forms (again), no more detection
- …
- Day 10: New version, return to day one. Crazy.
That’s the NeverEnding Story!!
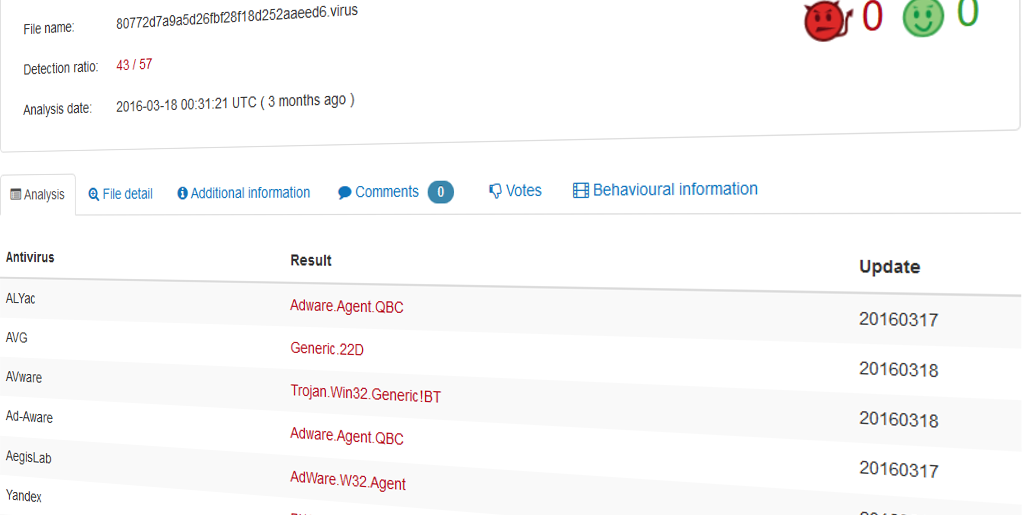
Here’s a picture taken on day 5:
I tried to tell them to change the method of whitelist, here’s the answer:
In relation to submission [3526780].
Regarding your question, we suggest you to do one of the following:
1. Sign your files with Class-3 digital certificates (X.509) from a Certificate Authority
2. Submit your software to SXXxx’s white-listing program:
https://Sxxxxxxx
Ok guys, what you are telling me is that I have to PAY to gain access to your whitelist? Is that how it works?
For information, a Class-3 certificate costs about 300$/year. Only medium/big companies can pay such a “thing” (that’s a sort of private key to identify a pair company-software). The others are condemned to be flagged by the AV vendors because they are not trusted.
EDIT: The second option is just a form to fill, at every release, to have the software whitelisted; It’s the same waste of time than with false positive forms. AVG gave us in the same time an FTP access to upload the binaries for every new release, that’s a lot better for us because it can be part of the compilation toolchain and doesn’t cost time. I wish the other vendor could do the same.
The worst, it would be really easy to whitelist a software that changes very often by creating a rule based on company name, software name, and a few signatures taken inside the software (.pdb debug information, strings, etc… )
Come on guys, I’m sure you can do better than telling software developers to buy a certificate.